I know what you’re wondering. Wangiri. What the heck does that mean?
It’s a Japanese word meaning ‘one (ring) and cut’. So called because fraudsters make one ring calls to consumers from high-rate overseas numbers. Curious consumers see a missed call from an overseas number and call it back, thus a call is made to the high-rate number and revenue is generated for the fraudster. The fraudster may attempt to keep the consumer on the call for longer via an Interactive Voice Response (IVR) system. Afterall, time is revenue in the dark world of telephony fraud.
That’s Wangiri, but what is Wangiri 2.0?
It’s like Wangiri but better, or worse, depending which side you’re on. A key difference is that Wangiri 2.0 is targeted at businesses rather than consumers. Furthermore, it’s a lot less obvious and can go undetected for months or even years. There are also a few flavours of Wangiri 2.0 to make things more interesting.
Be aware that you’re at risk whenever you collect phone numbers for the purpose of making a call or sending an SMS. Let’s take a deeper look at some common Wangiri 2.0 attacks
Contact forms (especially those used to request a call back or collected for sales purposes)
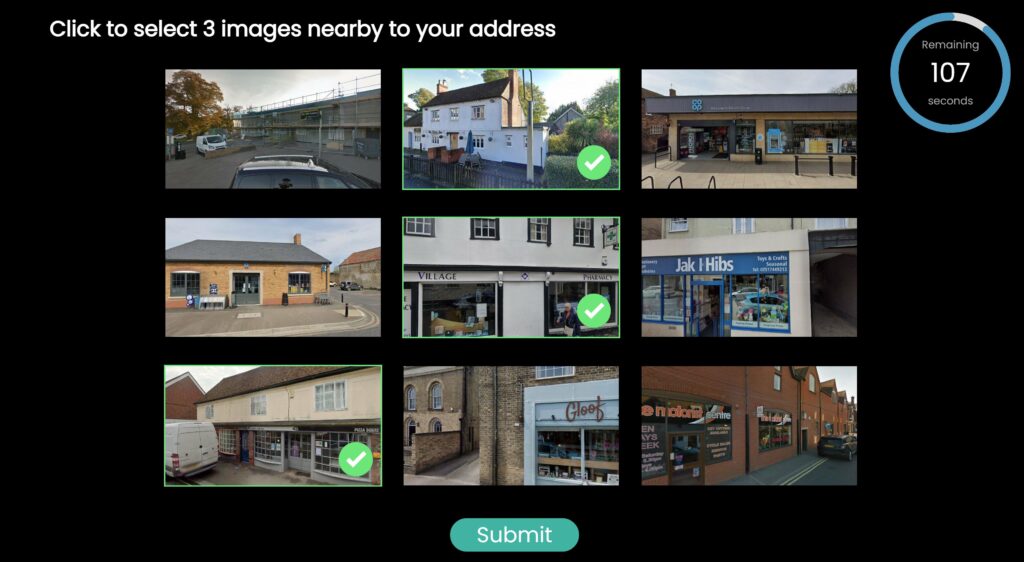
It starts with a simple online form and ends with a big phone bill. Fraudsters will complete your form and enter a high-rate overseas number to reach them on. Then do it again, and again, and you get the idea…
From there they just wait for you to dial the number. Larger companies and those operating internationally can be even more at risk since it might not be unusual to see an overseas number. Sales and business development teams usually have a higher likelihood of making outgoing calls to these numbers in the pursuit of following up on a hot new lead. To make matters worse it’s not uncommon for organisations to use an autodialer that initiates the call then subsequently connects a staff member. This removes the opportunity for due diligence to be performed prior to making a call.
Protect yourself from Wangiri 2.0
Enter your email address and we’ll send over some information on how to stay protected.
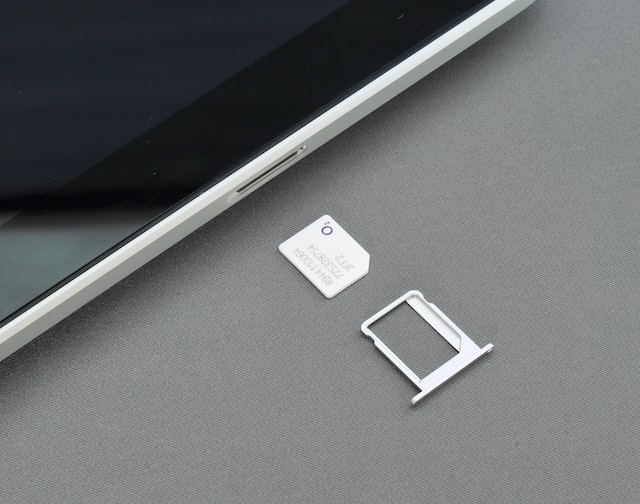
One-time passwords (delivered via voice or SMS)
Whilst one time passwords protect you from other types of fraud, they unfortunately create new opportunities for Wangiri 2.0. It’s an attack so simple it could be described as scary 😱. This attack happens when you collect phone numbers to push one-time passwords by SMS or voice call. The fraudster will signup to your service (often using a bot) and enter an overseas high-rate phone number. The SMS or call you make to issue the one-time passwords won’t be cheap and the fraudster will generate revenue with every code that’s sent. Thousands of one-time passwords sent to high-rate numbers will quickly ruin your day, and probably your budget too.
With both of these approaches fraudsters will write scripts to automate the process as much as possible. They will also use different numbers and may continuously trickle submissions into your system.
For many organisations this results in Wangiri 2.0 going undetected for quite some time. Costs won’t even be recognised as fraud, instead they are disguised under sales, marketing, customer service and hosting/operational costs.
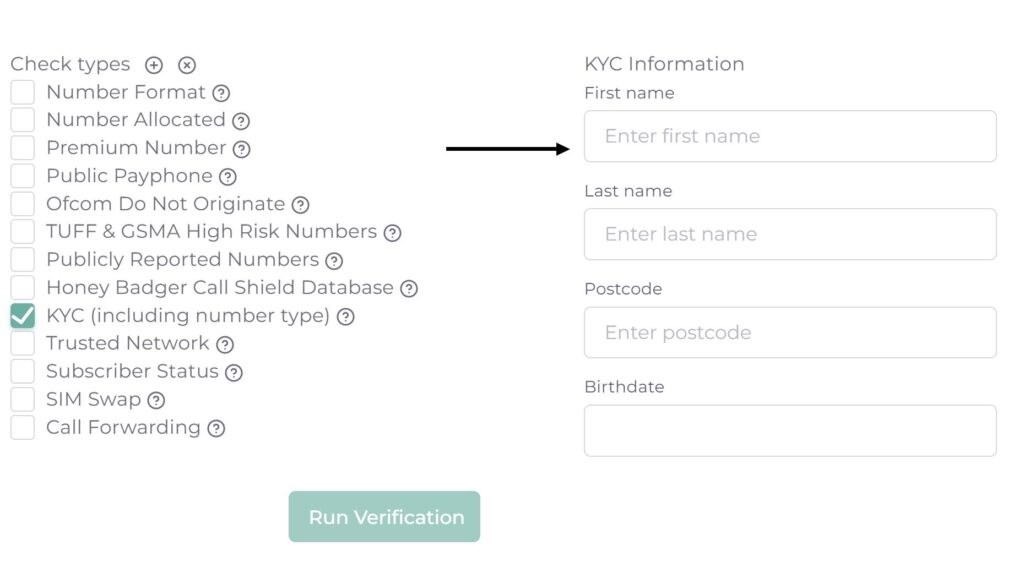
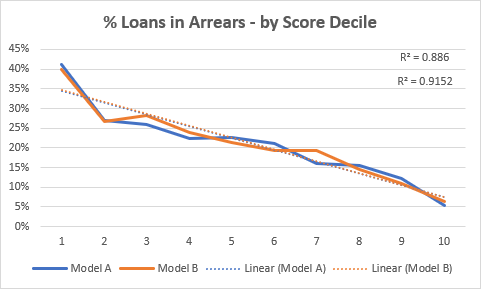
Of course, the savvy among us aren’t content with just being aware of Wangiri 2.0, we want to stop it too. Good news, Honey Badger can help. Our Number Intelligence service will scan phone numbers you’ve dialled previously to detect and measure the extent Wangiri 2.0 is happening in your organisation. Or, simply use our APIs or form validation widget to analyse numbers prior to form submission, sending an SMS or before making a call. Every phone number is instantly checked against millions of known high risk numbers and a risk score is returned.
Honey Badger HQ